In the wake of large-scale global events, cybercriminals are among the first to attempt to sow discord, spread disinformation, and seek financial gain. In February 2020, the World Health Organization (WHO) released an advisory warning of ongoing scams involving the ongoing outbreak of COVID-19, the disease caused by severe acute respiratory syndrome coronavirus 2 (SARS-CoV-2) and informally referred to as “coronavirus”. These scams aim to exploit people’s fear and uncertainty concerning the disease’s spread.
These can be broadly split into the following three categories:
Phishing and social engineering scams
Sale of fraudulent or counterfeit goods
Misinformation
While COVID-19 itself presents a significant global security risk to individuals and organizations across the world, cybercriminal activity around this global pandemic can result in financial damage and promote dangerous guidance, ultimately putting additional strain on efforts to contain the virus.
COVID-19 Phishing and Social Engineering Scams
Phishing is one of, if not the single most common attack techniques. Reports of email phishing campaigns using COVID-19-related lures surfaced almost immediately after confirmed infections began increasing in January 2020. Health organizations such as the WHO and US Centers for Disease Control and Prevention (CDC) have been prime targets for impersonation due to their perceived authority: Attackers have been observed tempting victims with URLs or document downloads using promises of important safety documentation or infection maps.
COVID-19 has also been a popular topic of discussion on cybercriminal forums. For example, in February 2020, a user initiated a thread on the prestigious Russian-language cybercriminal forum XSS to advertise a new COVID-19-themed phishing scheme. The user advertised a method to deliver malware via an email attachment disguised as a distribution map of the virus’s outbreak, containing real-time data from the WHO. The map itself is an impersonation of a legitimate map created by theJohns Hopkins Center for Systems Science and Engineering (CSSE). The offering was priced at $200 for a “private build”, and if buyers also required a Java CodeSign certificate, the price would be $700.
XSS post on COVID-19-related phishing scam
**!3Z8zm09A12I8vGAZJd4NtI! **
Legitimate Johns Hopkins COVID-19 distribution map
Another phishing scam, as detailed by Sophos, impersonated an official email correspondence from the WHO. The email contained a link to purported document on preventing the spread of the virus, but redirected victims to a malicious domain which attempted to harvest credentials. The email contained several grammatical and format errors, which can be used by attackers to narrow down their victims and bypass spam filters. We discussed this technique in our blog on The Ecosystem of Phishing.
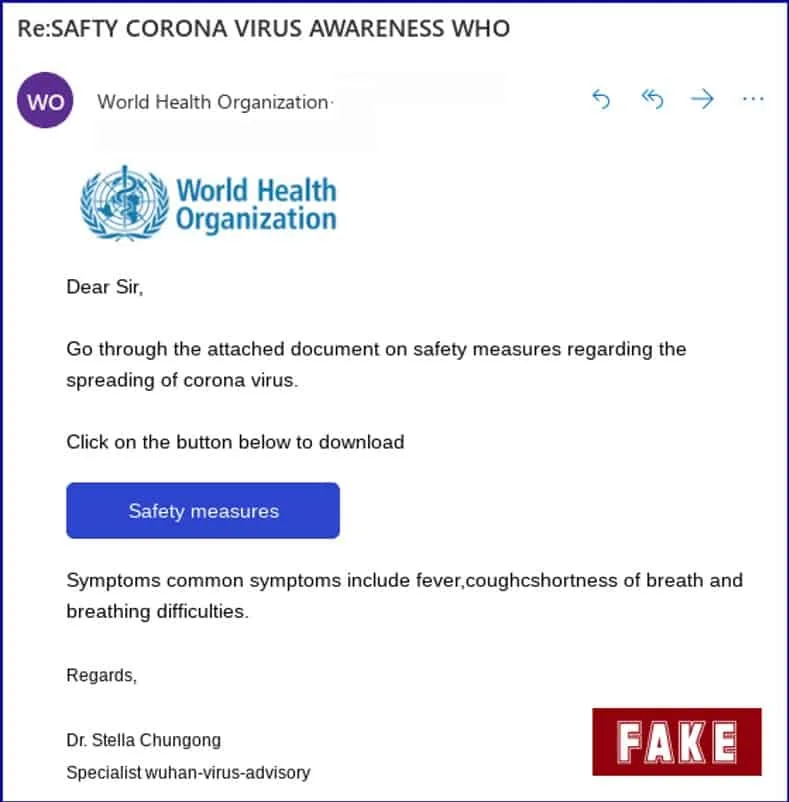
Phishing scam impersonating the WHO (Source: Sophos)
These campaigns are often targeted towards geographies which have significant numbers of COVID-19 infections. In late January 2020, a phishing campaign targeted individuals in Japan with emails claiming to be from disability welfare service providers and public health centers. The emails used lures of documents containing information on alerts of new COVID-19 infections as well as preventative measures against the virus. However, when accessed, the documents attempted to download and install Emotet, an information stealing malware. Similarly, individuals in Italy, which has the highest number of confirmed infections of COVID-19 outside of China, were targeted by a phishing campaign in March 2020 which impersonated WHO officials and attempted to distribute the Trickbot trojan.
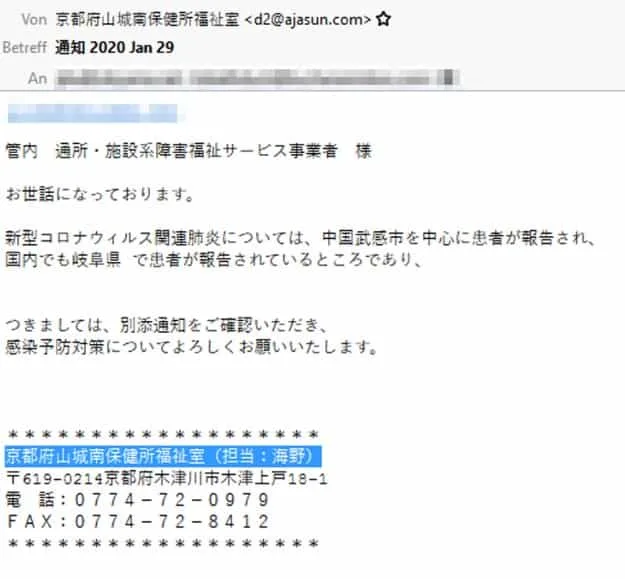
Japanese-language phishing email (Source: IBM)
**!6V1a37v5nQfI7gB3SZfAyZ! **
Italian-language phishing email (Source: Sophos)
Organizations like the WHO or CDC are also not the only ones at risk of being impersonated. Since January 2020, the number of COVID-19-related domains registered has increased significantly: Digital Shadows (now ReliaQuest) has identified over 1,400 domains registered over the past three months. While many of these are likely legitimate and dedicated to providing information on the virus and its spread, it is almost certain that a portion have been created with malicious intent. Malicious domains can be used to spread misinformation, host phishing pages, impersonate legitimate brands, and sell fraudulent or counterfeit items. In March 2020, the UK’s National Fraud Intelligence Bureau (NFIB) reported over 21 cases of COVID-19-related fraud schemes, resulting in losses of over £800,000 in the UK alone. The NFIB cited specific examples which included the fraudulent sale of face masks and sites which promised victims a map of COVID-19 infections near them in return for a bitcoin payment.
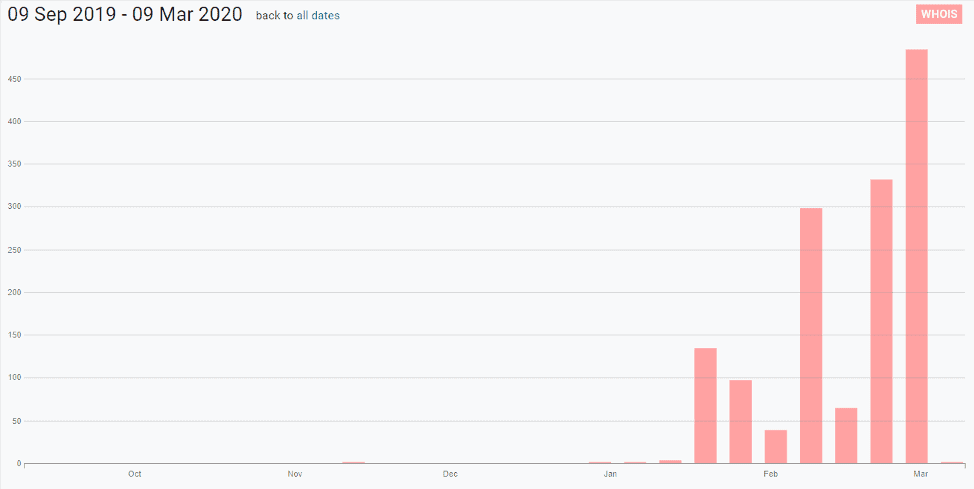
COVID-19-related domains registered over the past six months (Source: Digital Shadows (now ReliaQuest)’ Shadow Search (now ReliaQuest GreyMatter Digital Risk Protection))
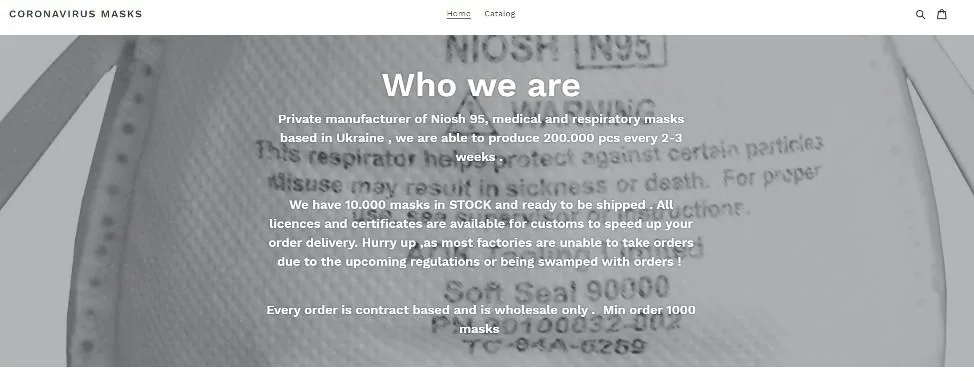
Potentially fraudulent site offering discounted face masks
Even domains which contain no overt references to the virus have been identified. Below is an example on Pastebin that uses the lure of a purportedly infected Italian footballer to direct individuals to a malicious site.
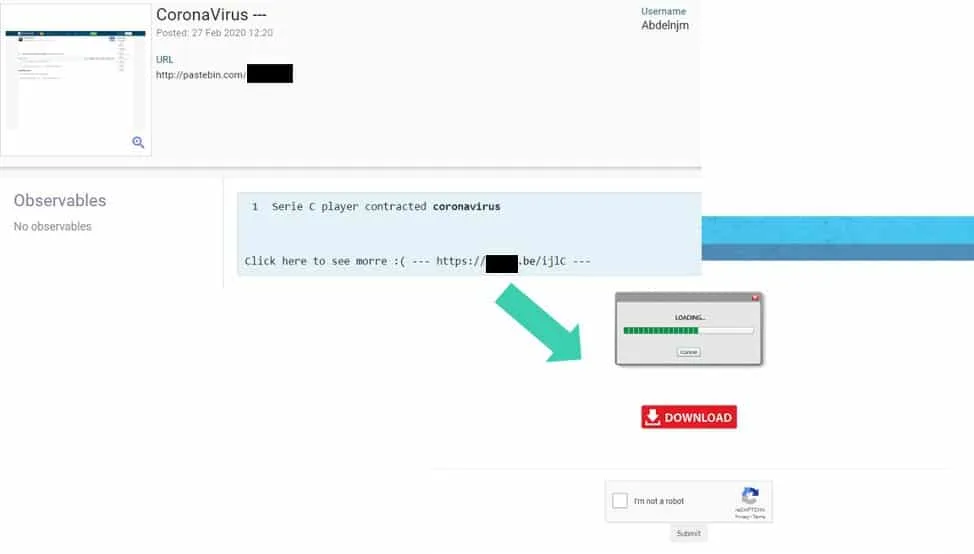
Pastebin post with a malicious COVID-19-related link (Source: Digital Shadows (now ReliaQuest)’ Shadow Search (now ReliaQuest GreyMatter Digital Risk Protection))
COVID-19 Fraudulent and Counterfeit Goods
The COVID-19 outbreak has contributed to a global shortage of healthcare equipment. Supplies like face masks and hand sanitizer have been out of stock at many major retailers, and prices on ecommerce websites have in some cases tripled over the past few weeks. This shortage is likely in part driven by the spread of misinformation. Face masks are essential for the safety of medical staff but have little effect on preventing healthy individuals from infection: TheWHO recommends face masks should not be used unless caring for an individual with a suspected COVID-19 infection.
China is the world’s largest global supplier of medical face masks, manufacturing approximately 80% of face masks worldwide. Due to the COVID-19 outbreak, production and exports from China have been severely limited over the past few months. This has put a strain on manufacturers outside of China, creating a market for counterfeit products and fraudulent listings.
As mentioned earlier, hundreds of potentially shady websites have popped up that claim to offer heavily discounted face masks. Even if the products are legitimate, there is no guarantee that the products even exist to begin with.
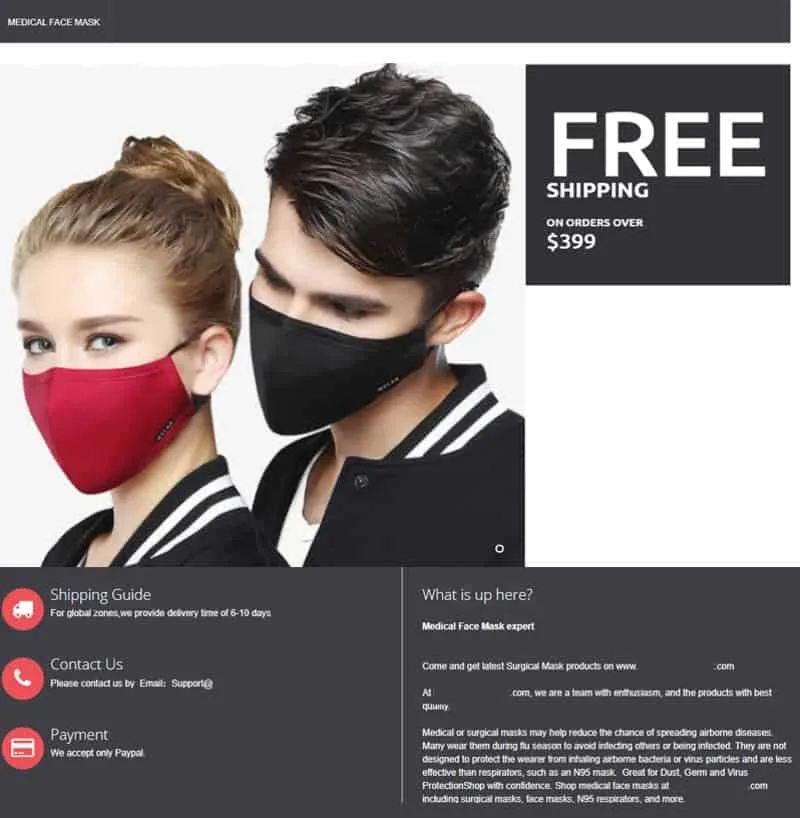
Website selling discounted face masks
Medical equipment has even been observed for sale on cybercriminal marketplaces. Listings on Empire, an English-language dark web marketplaces, specifically mention COVID-19 to help push their goods. One listing offers 2,000 boxes of surgical face masks for $6,500. Vendors like these typically engage in the sale of illicit drugs, but have clearly seen a market opportunity to branch out into medical equipment.
**!3K9hanQuyOnIweeb6G9ikr! **


Listings for face masks on Empire market (Source: Digital Shadows (now ReliaQuest)’ Shadow Search (now ReliaQuest GreyMatter Digital Risk Protection))
COVID-19 Misinformation / Infodemic
COVID-19-related misinformation has primarily been spread via social media and private messaging platforms. Misinformation does not always have the same tangible financial impact as other types of cybercriminal activity, but it can still be used to cause panic, incite racism and xenophobia, promote harmful at-home cures, and result in shortages of supplies and critical medical equipment. The WHO has labelled this proliferation of information – both legitimate and not – as an “infodemic”, and have assembled a dedicated team to manage the spread of potentially harmful misinformation.
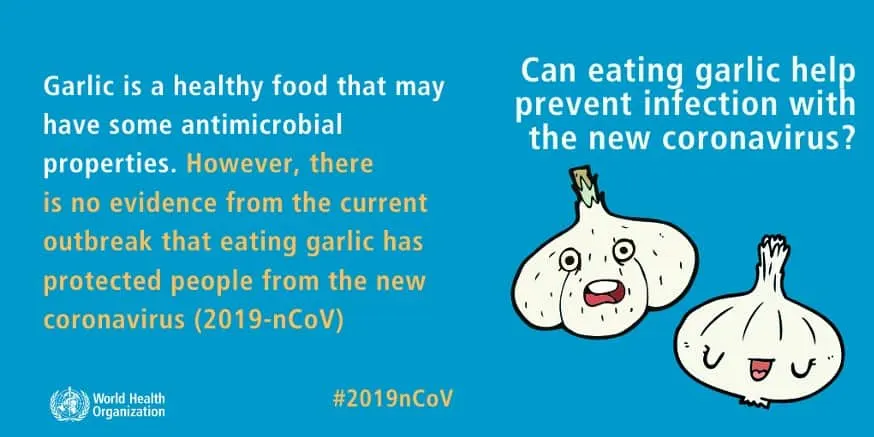
WHO graphic debunking at-home cures (Source: WHO)
Official government entities have also taken steps to curb misinformation. Below is a tweet from the official account for the spokesperson of the Government of Kenya denouncing the spread of misinformation.
Additionally, an Australian Member of Parliament also denounced a fraudulent social media post that was impersonating the Australian Department of Health, advising individuals to avoid areas populated with Chinese nationals.
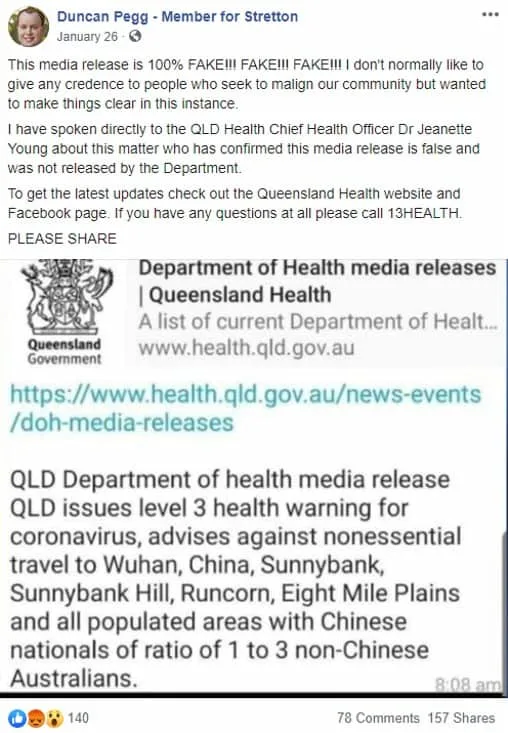
Australian MP denouncing the spread of misinformation
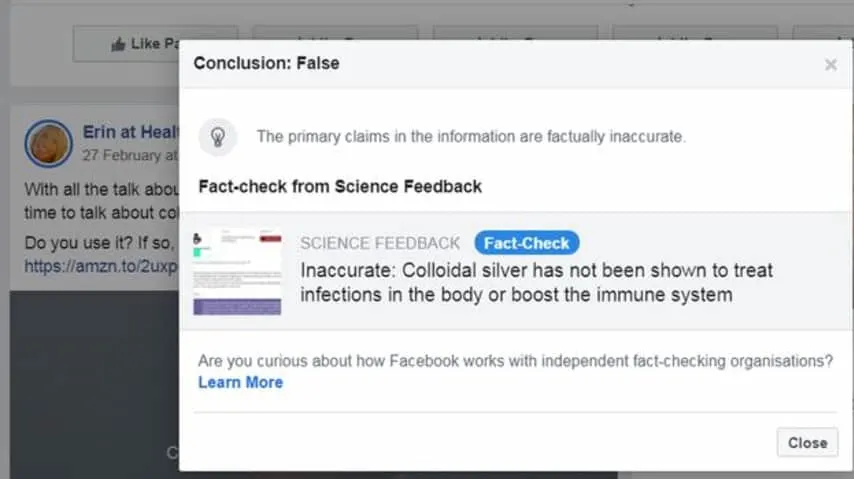
Social media platforms themselves have also taken a proactive approach to help prevent the spread of false information related to COVID-19 by flagging posts which may be illegitimate and hiring third-party organizations to fact-check posts. When searching COVID-19-related terms on platforms like Twitter, Facebook, and even Instagram, users are prompted to obtain information from official sources. This can even help streamline the dissemination of legitimate information by providing centralized results.
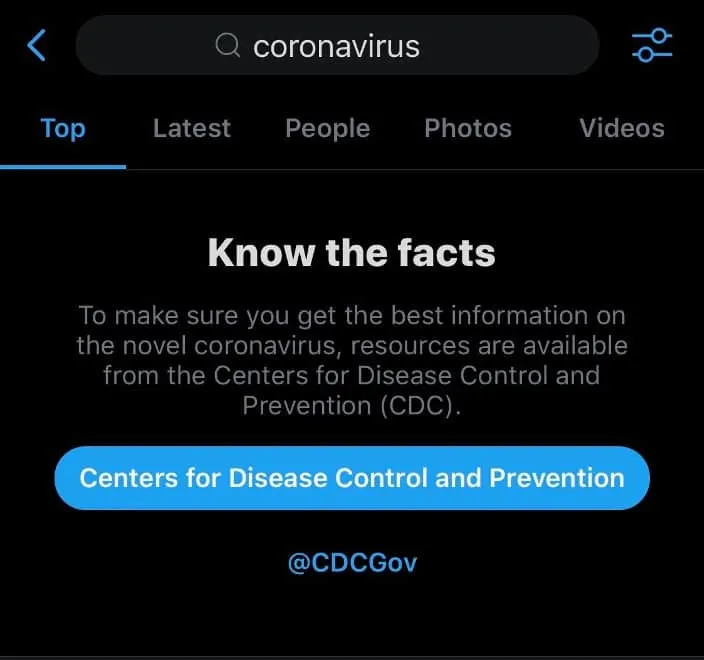
Twitter search directing users to the official CDC account

Facebook search directing users to the official CDC website

Instagram search directing users to the official WHO and UNICEF accounts
Search engines like Google have also manually intervened to help fight the spread of misinformation: When searching for COVID-19-related terms, users are provided an “SOS Alert”, which includes news articles from legitimate, vetted outlets and links to official resources from the CDC and WHO.
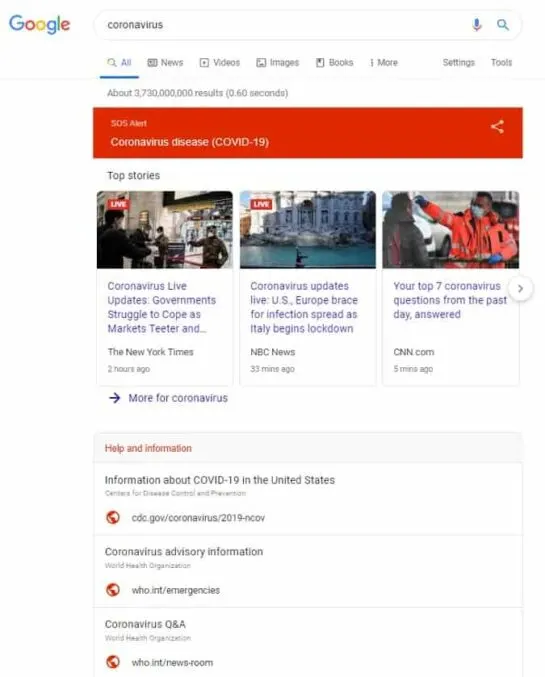
COVID-19 “SOS Alert” on Google
These measures are a great step in the right direction, and have likely already stopped the distribution of a significant amount of harmful material. Organizations have become more aware of the risks of the spread of misinformation over the past year, but there is still onus on users to ensure that the information they digest and share is legitimate. This is particularly important during global health crises, where the ramifications of misinformation can be deadly. For example, some recipes for making homemade hand sanitizers are not suitable for use on skin and can be ineffective in halting the transmission of COVID-19.
Example of potentially dangerous at-home cures (Source: BBC)
COVID-19: Staying Safe On and Offline
To help prevent the spread of misinformation, individuals should ensure that they only follow guidance from official national health institutions like the CDC and NHS, as well as international organizations like the WHO.
The WHO recommends the following basic protective measures to prevent the spread and contraction of COVID-19:
Clean your hands frequently with an alcohol-based hand rub or wash them with soap and water.
Maintain at least 1 meter (3 feet) distance between yourself and anyone who is coughing or sneezing.
Avoid touching your eyes, nose, and mouth.
Practice respiratory hygiene: Cover your mouth and nose with your bent elbow or tissue when you cough or sneeze and dispose of used tissues immediately.
Stay home if you feel unwell. If you have a fever, cough, and difficulty breathing, seek medical attention and call in advance. Follow the directions of local health authorities.
Use fact-checking tools to challenge potentially dubious claims on social media.
Be wary of unsolicited correspondances that contain alarmist messaging and/or impersonate official health and safety institutions. Grammatical and formatting errors can help you identify malicious phishing emails.
Be wary of emails soliciting charitable donations.
Do not download files or visit unknown websites linked in unsolicited emails.
Do not purchase medical equipment from unofficial third-party vendors (particularly on the dark web!). If a deal seems too good to be true, then it probably is.
Additional official resources:
COVID-19 Q&A (WHO)
COVID-19 overview (WHO)