Year: 2015

Criminal Services – Crypting
December 18, 2015 | 3 Min Read

‘Hacker Buba’: Failed extortion, what next?
December 11, 2015 | 2 Min Read

Communicating Intelligence: The Challenge of Consumption
December 10, 2015 | 4 Min Read

Communicating Intelligence: Getting the message out
December 8, 2015 | 4 Min Read
TalkTalk Information Likely to be Discoverable on The Dark Web
December 4, 2015 | 3 Min Read

Communicating Intelligence: A Battle of Three Sides
December 2, 2015 | 2 Min Read

Criminal Services – Counter Antivirus Services
November 30, 2015 | 4 Min Read

Activity Based Intelligence – Activating Your Interest?
November 25, 2015 | 4 Min Read

Crackas With Attitude: What We’ve Learned
November 23, 2015 | 3 Min Read

The Way of Hacking
November 10, 2015 | 3 Min Read

Emerging Markets: Online Extortion Matures via DDoS Attacks
November 9, 2015 | 5 Min Read

Crackas With Attitude strike again?
October 28, 2015 | 2 Min Read
TalkTalk: Avoiding The Hype
October 28, 2015 | 4 Min Read

Smilex: Dangers of Poor OpSec
October 27, 2015 | 3 Min Read

Online Carding
October 7, 2015 | 4 Min Read

How the Internet of Things (IoT) is Expanding Your Digital Shadow
September 9, 2015 | 2 Min Read

The Intelligence Cycle – What Is It Good For?
September 9, 2015 | 10 Min Read

OPSEC and Trust In An Underground Cybercriminal Forum
September 9, 2015 | 4 Min Read

Digital Shadows Invited To 10 Downing Street
September 8, 2015 | 2 Min Read
Interest in London’s burgeoning tech industry is growing so rapidly that even David Cameron has taken notice; at Pitch10, an event at 10 Downing Street to be held on Thursday 31st July, ten of the most promising digital companies in Britain will pitch...

Working In Multilingual Sources
September 8, 2015 | 5 Min Read
This post will be about some of the challenges you are likely to face trying to handle data in different languages and how to deal with them. Most of our code is in Java so the examples here will all be written in...
The Intelligence Trinity
September 8, 2015 | 5 Min Read
For several years now there has been considerable hype and hubris around the term ‘intelligence’ within the cyber security industry. It feels as if the term has been diluted as its usage has extended to include vendors dealing in a range of issues from...

Source Evaluation
September 8, 2015 | 5 Min Read
To organisations, threat intelligence is about understanding the threat landscape – the various actors and campaigns which conduct cyber attacks – so that when they are specifically targeted it can be detected, mitigation put in place, and the risk to...

Digital Shadows joins roundtable at 10 Downing Street
September 8, 2015 | 1 Min Read
Alastair Paterson, CEO of Digital Shadows, recently visited 10 Downing Street to participate in a roundtable on cyber security. The session brought together leaders from industry, academia and government and sought to address the challenges surrounding...

Remote working at Digital Shadows
September 8, 2015 | 6 Min Read
Here at Digital Shadows we’ve worked hard to assemble the most dedicated and talented development team possible and that has resulted in our team being concentrated here in London, but including members both further afield in the UK and internationally....

Analytical Tradecraft at Digital Shadows
September 8, 2015 | 3 Min Read
This week my colleague and I attended the SANS Cyber Threat Intelligence conference in Washington DC. It was great to hear more from analysts and CTI users from across the community, as well as mingle with the plethora of vendors who were present. This...

Digital Shadows Works Alongside Bank of England To Develop New Testing Framework To Help Guard UK Financial Sector Against Cyber Attack
September 8, 2015 | 4 Min Read

The Dangers of Groupthink
September 7, 2015 | 4 Min Read
Over the next few blog posts we’ll be looking at various types of cognitive bias and suggest ways of dealing with...

The Dangers of Groupthink: Part 2
September 7, 2015 | 5 Min Read
This post moves on to the second cause of groupthink and tries to understand how organizational structural faults may result in manifestations of...

The Adult Friend Finder Breach: A Recap
September 7, 2015 | 5 Min Read
Last week, news quickly spread about a security breach that impacted the casual dating website Adult Friend Finder. Will Gragido. Head of Threat Intelligence for Digital Shadows in the USA, shares his...
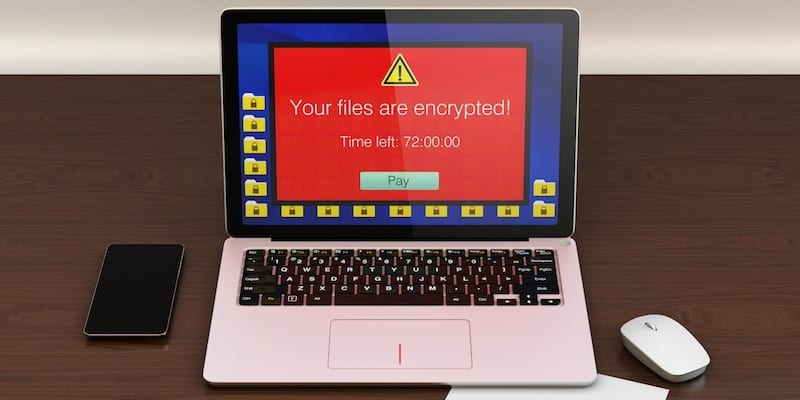
Emerging Markets & Services: Ransomware-as-a-Service
September 7, 2015 | 5 Min Read
A look at emerging markets and services, specifically at ...

Kaspersky Labs Discloses Duqu 2.0 Attack
September 7, 2015 | 4 Min Read

Digital Shadows Integrates With Maltego Through Partnership With Malformity Labs
September 7, 2015 | 4 Min Read
What’s In a Name? The Mystery Surrounding the Identity of the Actors Responsible for the Saudi Arabia Breaches
September 7, 2015 | 6 Min Read

Online Extortion – Old Ways, New Tricks
September 7, 2015 | 6 Min Read
Extortion is nothing new for organised crime. For centuries, gangs have been operating protection rackets and kidnappings to successfully extract ransom money from their victims. And as with many things in modern life, these old techniques have been...
Exciting Times, Exciting Team at Digital Shadows
September 4, 2015 | 4 Min Read
Yesterday we announced that Stuart McClure, founder and CEO of Cylance, Inc, is joining our Board of Directors. The entire company is excited about his joining us, and James Chappell and I are especially looking forward to working with him as we further...

Digital Shadows and ThreatConnect Partner to Help Customers Improve Security Defenses
September 4, 2015 | 2 Min Read
One of the foundational values of Digital Shadows is the appreciation and value we put on our collaboration with customers and our coordination with our strategic business partners. It is because of this value that we’re delighted to announce today that...

Exploiting Is My Business…and Business Is Good
September 4, 2015 | 8 Min Read
In 2015 we are seeing new trends emerge with respect to Exploit Kits in the wild. These trends are particularly interesting in that they suggest that the frequency of 0-day exploits made available in these kits is growing while the time to integrate said...

